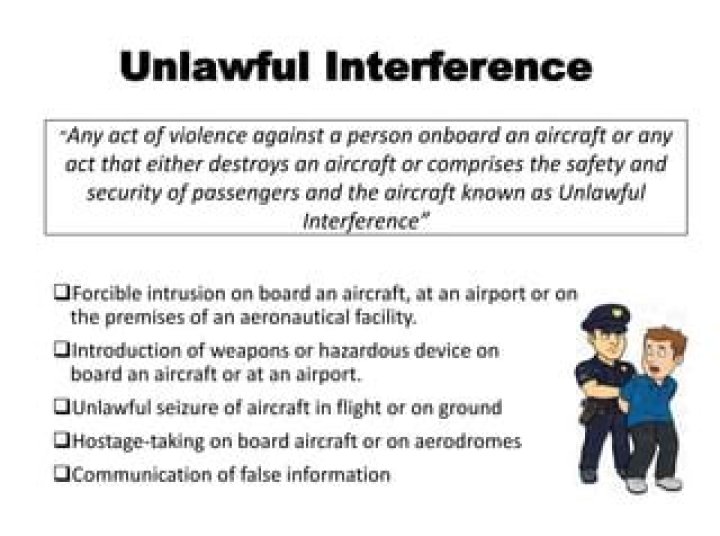
What is unlawful interception?

Andrew Mclaughlin
Published Mar 21, 2026
(b) A person commits an offense if the person: (1) intentionally intercepts, endeavors to intercept, or procures another person to intercept or endeavor to intercept a wire, oral, or electronic communication; (2) intentionally discloses or endeavors to disclose to another person the contents of a wire, oral, or …
What is an interception warrant?
• A targeted interception warrant (see section 15(2) of the Act) authorises or. requires the person to whom it is addressed to intercept the communications described in the warrant and/or obtain secondary data.
How does lawful interception work?
Lawful Interception (LI) refers to the ability of law enforcement to eavesdrop on users of communication networks providing they have the authority to do so. It is the government’s legally-sanctioned access to private communications, such as telephone conversations, e-mail messages, direct messages, and the like.
What is government interception?
The interception of communications includes listening to the calls made on a telephone or opening and reading the contents of a target’s letters or e-mails.
Is it illegal to intercept email?
Although interception of email transmission—that is, snooping while an email is in “real-time” transmission between sender and receiver—is a federal crime under the Electronic Communications Protection Act (ECPA) (18 U.S.C.A 2517(4)), it has been accomplished by hackers.
What states can you not record phone calls?
Massachusetts (only “secret” recordings are banned, but is the only state without a “public location” exception) Montana (requires notification only) New Hampshire. Oregon* (One party for electronic communications, two party for in-person conversations)
How long does an interception warrant last?
Duration of interception warrants A warrant issued under the urgency procedure (on any grounds) is valid for five working days following the date of issue unless renewed by the Secretary of State. 3.18 Upon renewal, warrants issued on serious crime grounds are valid for a further period of three months.
What is illegal interception of communication?
intentionally discloses, or endeavors to disclose, to any other person the contents of any wire, oral, or electronic communication, knowing or having reason to know that the information was obtained through the interception of a wire, oral, or electronic communication in violation of this subsection; (d)
What’s another word for interception?
In this page you can discover 9 synonyms, antonyms, idiomatic expressions, and related words for interception, like: interposing, blocking, interfering with, capture, interference, stopping, intercept, electronic surveillance and electronic-communications.
What are interception systems?
Lawful interception (LI) refers to the facilities in telecommunications and telephone networks that allow law enforcement agencies with court orders or other legal authorization to selectively wiretap individual subscribers. As with many law enforcement tools, LI systems may be subverted for illicit purposes.
Can police intercept calls?
IMSI-catchers, also known as Stingrays, allow police forces to track mobile phones and intercept text messages, calls and other data within their radius in real time. The devices can capture the private data and phone calls of anyone who happens to be in range, whether they are a suspect or not.
Is sending emails without permission illegal?
So to reiterate: It is legal in the U.S. to send an unsolicited commercial email. You do, however, have to comply with certain rules when sending those unsolicited emails, and if you don’t, the penalties can be very serious. Follow these five simple guidelines, and stay on the right side of the CAN-SPAM Act.
Are our emails monitored?
Emails sent or received through a company email account are generally not considered private. Employers are free to monitor these communications, as long as there’s a valid business purpose for doing so.
Who Authorises intrusive surveillance?
1.2 ‘Directed surveillance’ and the use of ‘covert human intelligence sources’ require the lesser control of self-authorisation from a designated person within the agency undertaking the action;[1] whereas, ‘intrusive surveillance’ requires approval from a High Court judge acting as a Commissioner before it can take …
What is covert surveillance?
Surveillance is covert if it’s done in a way that tries to ensure the subject is unaware it is, or could be, taking place. Covert surveillance is divided into two categories, both of which are subject to the Covert surveillance and property interference code of practice.
What is 18 US Code 2511?
Section 2511 of Title 18 prohibits the unauthorized interception, disclosure, and use of wire, oral, or electronic communications. Consequently, unless an interception is specifically authorized, it is impermissible and, assuming existence of the requisite criminal intent, in violation of 18 U.S.C. § 2511.
chapter 5, to intercept a wire, oral, or electronic communication transmitted by radio or to disclose or use the information thereby obtained. (e) It is unlawful to intercept any wire, oral, or electronic communication for the purpose of committing any criminal act.
What intercepted communication?
“intercept”, in relation to a communication, means listening to, monitoring, viewing, reading or recording, by any means, such a communication in its passage over a tele- communications network without the knowledge of the person making or receiving the communication; Act inconsistent with Constitution.
What is another word for interception?
| obviation | deterrence |
|---|---|
| thwarting | forestalling |
| prevention | preclusion |
| avoidance | determent |
| obstruction | blockage |
What are the federal laws for lawful interception?
In the United States, three Federal statutes authorize lawful interception. The 1968 Omnibus Crime Control and Safe Streets Act, Title III pertains mainly to lawful interception criminal investigations.
When does a person acting under color of law intercept?
(3) a person acting under color of law intercepts: (A) a wire, oral, or electronic communication, if the person is a party to the communication or if one of the parties to the communication has given prior consent to the interception;
How is lawful interception different from mass surveillance?
Lawful interception differs from the dragnet -type mass surveillance sometimes done by intelligence agencies, where all data passing a fiber-optic splice or other collection point is extracted for storage or filtering. It is also separate from the data retention of metadata that has become a legal requirement in some jurisdictions.
Is there a global treaty for lawful interception?
The principal global treaty-based legal instrument relating to LI (including retained data) is the Convention on Cybercrime (Budapest, 23 Nov 2001). The secretariat for the Convention is the Council of Europe. However, the treaty itself has signatories worldwide and provides a global scope.